I’m not sure what your objections are? I don’t mean this in a rude way, I just may be miss-reading your objections.
The diagram is linked via URL, so I thought its source should be clear (right click, copy link) - but will edit the post to makes its source clear. I didn’t copy the diagram and upload it, I wasn’t trying to hide where it came from.
The comments in the block I thought I made clear were from another user in the forum that I linked at Audiophile style. I.e. one person thought he had broken the MQA authentication and another user told him he hadn’t. I.e. I wrote: “And a later user explains:” before going into the block quote.
If you wish to have proper citations in Chicago Style (16) I can do that, but I thought the sources were clear for an internet forum!! 
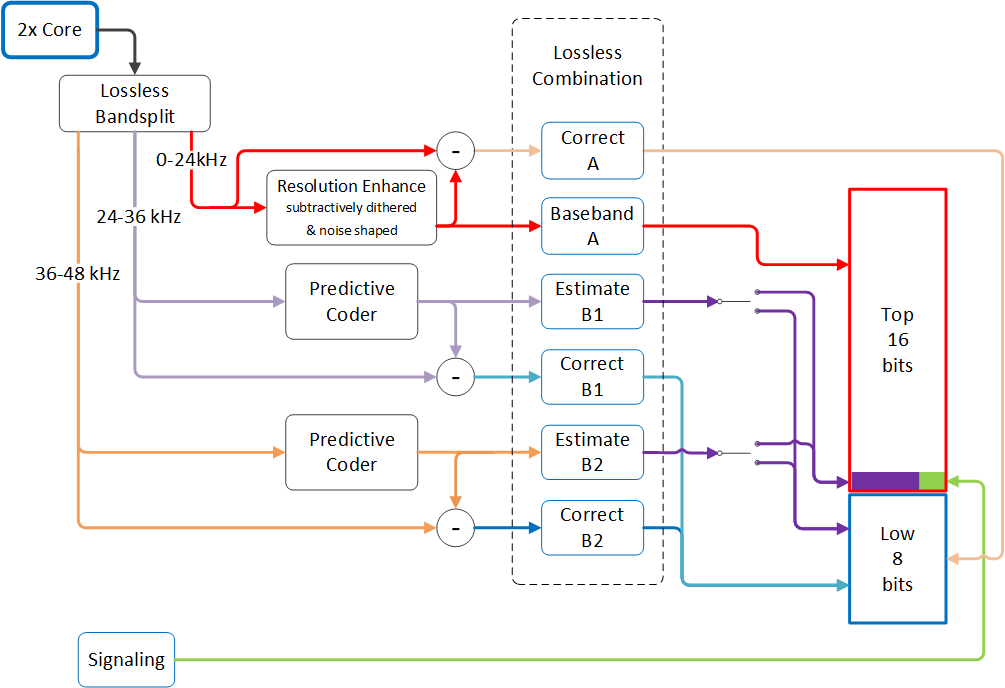
I put the block diagram in to try further illustrate why you can “Bit truncate” an MQA file and it keeps its authentication. The diagram shows the top 16 bits is the part of the music our ears hear i.e. 24kHz and below. It was an expansion/diagram of what the block text section was saying. Whilst the diagram is mainly concerned with how MQA files “fold” music, I thought it was a useful visual representation. Maybe I should have just sniped the Top 16 bits/Low 8 Bits of the diagram to save confusion.
If you are referring to this paper: AES E-Library » A Hierarchical Approach to Archiving and Distribution they are not using the term archiving in the same manor as I am. Are you referring to a different paper? I don’t recall any others talking about archiving in the way I was describing.
However, I will be honest: I am struggling to find my source for MQA being part developed for being an archival format because of its authentication. Over the past few weeks I’ve watched numerous videos, read websites and papers on MQA. I have kept a log of interesting bits to Cite. The long term storage part I remember coming up as I am researching “The Digital Dark age” for work right now so it stuck in my mind. But I think its still a point that stands, the authentication process helps against bit-rot with upcoming digital dark age (or, thinking more about it - might make it worse as the public key to decrypt it might be lost!).
I’ve already touched on why I put the diagram in. The diagram is nothing to do with marketing.
On the marketing I may have then done a 2 + 2 = 5 approach. My brain went: “Because they had this cool solution to bit rot - someone thought they could use this tech as a marketing tool” and hence we have the name Master Quality Authenticated and different lights on our decoders etc. I am speculating about this. But I do wonder if the authentication lights and ideas came after the original idea of having the file authenticated.
Hope that helps? Its very late were I am, so won’t respond till tomorrow if you have further questions.
Sorry I caused confusion.