So then Roon ARC is also not suitable for you, because port forwarding is the current mechanism used by it.
Perhaps you should be more concerned about this than ARC, especially if you don’t know what it is. ![]()
As I’ve said before, most attacks occur as a consequence of the user inadvertently running malicious software.
I’ve finally decided to add my phone to Tailscale and use ARC that way. No ports open and my Synology NAS remain off the internet but, can be accessed via Tailscale.
Do you have this working with iOS or Android?
Understood. 113 is a leftover from days past. One could set up a port forward to nowhere way up in your internal IP Adress range
I’m not @Formula, but … ARC over Tailscale works on Android. I don’t have iOS to test.
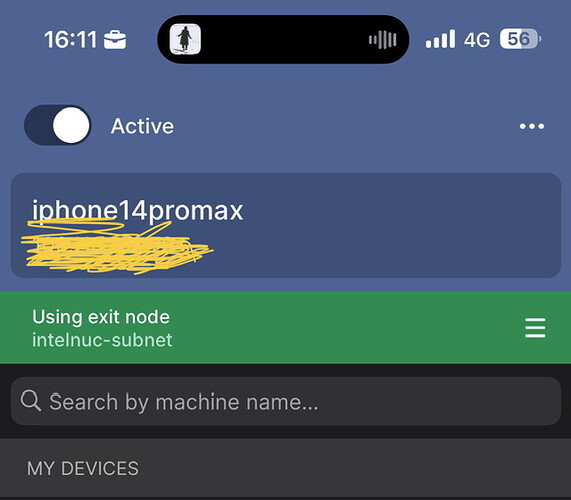
Yes I do. I’ve reused my NUC8i5, hackintoshed it and run it as an Exit Node in order to access my network.
On my phone I choose activate and exit node.
Thanks @Formula and @Fernando_Pereira.
This incentivized me to rethink how I access Roon from outside my home. I’ve played with various strategies in the past but haven’t been thrilled with any of them.
Thinking about what you two do made me realize that I could probably stand up a WireGuard VPN on my UniFi UDM Pro and use that to access ARC from an iPhone. Took just a couple of minutes to get that working. Surprisingly, Roon Remote seems to be working with this same setup including discovering the iPhone as an endpoint. I didn’t expect that to work.
I’ll play with this more but even if just ARC runs reliably this way, it’s a far more secure approach then mapping a public port.
Thanks for pointing me in the right direction!
It may be more secure, but it still opens a listening port.
Of course.
I’ll take a hardened, cryptographically secured, peer-reviewed VPN endpoint over a TCP/UDP mapped port to Roon any day of the week. UniFi also supports push notifications for client VPN changes which makes it easy to monitor connections though good luck connecting to a WireGuard endpoint without a legitimate key.
Every communication outside of your network opens ports. It’s about minimizing that (how many, directionality, how long they are open, etc.) and having a port or two open for VPN only is a good way to do that. VPN is the only external access I allow to my network and that is only allowed from devices with dedicated, password protected certs.
Yes easily done
8 posts were split to a new topic: Is there a “correct” or best practice way to use ARC to avoid problems