When QNAP “contacted Roon”, they contacted @crieke, not us. I spoke to @crieke as soon as I saw this post, and he had identified the issue and was already working on a fix. The fix came hours later. The code affected is not code we wrote/own/maintain. @crieke has our full support, and even has access to our private Slack server, where he has a direct line of priority access to myself and the rest of our team. My communication with him was via this Slack, where he responded to me within seconds.
I reached out to @crieke who not only had identified a issue, created a fix, but also posted here with transparent and informative information. I made his post “staff colored”, but did not add anything further because there was no further information for me to add. He was on it.
You have confused two matters.
- QNAP users are being targeted by ransomware due to weak passwords
- this issue with the Web UI on the QNAP’s Roon QPKG
They are unrelated. They were just announced at the same time.
The issue was a “sanitization bug” in @crieke’s web UI for QNAP, not RoonServer, as the advisory states. No changes are planned to be made to RoonServer which remains safe.
The sanitization bug can only be dangerous if the outside world has access to your QNAP’s admin interface.
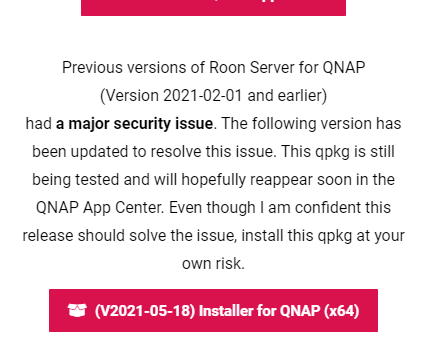
@crieke has posted a fix and asked QNAP to reinstate his package.
This sounds like a message from a support person who is not involved in the process of re-approval of the QPKG in their “app store”. I wouldn’t read too much into it.
RoonServer is supported by Roon, and can be downloaded at roonlabs.com/downloads – it will work on QNAP and other NASs, but may require custom installation into those systems. This is something Roon does not provide support for.
Roon on QNAP and other NASs is community supported by @crieke. He maintains a site for this here: Roon on NAS.
Here, I have found a link for “(PreRelease) Installer for QNAP (x64)” – I assume this is the “manual” method.
@crieke, can you please comment about the manual process?